Stages of JavaScript grief
3 May 2016 - 4:24pm — BevanThis is one of my favourite blog posts of all time. It is no longer published, but I found it on the wayback machine (internet archive). I am reposting it here for your enjoyment. I hope the original author doesn't mind.
Originally by By Dan Lee, 9 September 2010.
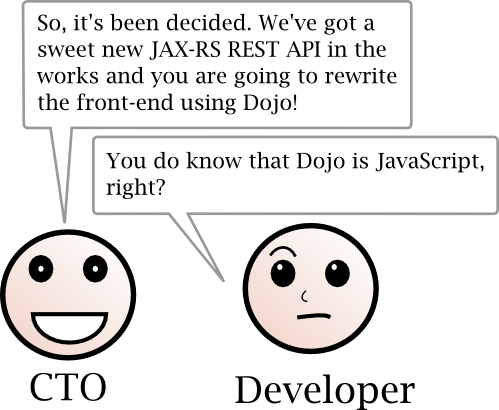
The typical beginning of an Enterprise Developer’s JavaScript education is involuntary in nature. In many cases an engineer with a strong background in Java, or other strongly-typed languages, is informed that their next project requires JavaScript. Like all forced actions, this will be a bumpy road. So bumpy in fact, that the Enterprise Developer will go through a grieving process as they leave behind their beloved strongly-typed language and plunge into the duck-typed world of JavaScript. This process of grief has four distinct stages.
Stage One: Doubt
As I discussed earlier, the Enterprise Developer’s usual introduction to JavaScript is less than stellar. Rightly so, when a developer hears that the next ‘Big Project’ will be done in JavaScript, their first thoughts are of the skeptical variety.
- Sufferer will indicate that the prospect of using JavaScript will certainly lead to folly.
- Sufferer will be heard saying things like, “JavaScript? Isn’t that the thing hackers use to screw up your Back button so you can’t leave a page?”
Terms of engagement template for freelancers
14 December 2015 - 7:44pm — BevanMost people who have worked as freelancers for a while will have a story about a client who never paid. Often freelancers just do not have the time to think about getting a lawyer or writing a contract. Indeed the costs of getting a lawyer involved usually outweigh the risks for most freelancer engagements.
However many times, all the freelancer needs is that the client understands how they roll: the terms of how they engage. To avoid getting burned, I require my clients to either prepay the hours or sign my terms of engagement.
Backcountry ski touring insurance in Canada
13 December 2015 - 12:07pm — BevanI researched and compared travel insurances that include cover for backcountry ski touring for 28 days in Canada for a NZ-resident couple in their thirties. Most travel insurers exclude skiing outside of the ski area, or off-piste. These are the options I found. Most also offer annual options which are comparable to 4-week single trips.
DISCLAIMER: I am not qualified to give financial advice.
Tugo, via Alpine Club of Canada
Security vulnerabilities in UserPro plugin for WordPress
1 May 2015 - 4:43pm — BevanUserPro plugin for WordPress versions up to 2.28 have multiple security vulnerabilities that expose the website they are installed on to a wide scope of attack vectors. The plugin has 27 occurrences a procedure call that is extremely insecure (extract($_POST)) and a futher 57 probably insecure uses of extract().
Your Drupal website has a backdoor
22 October 2014 - 3:09pm — BevanI estimate hundreds of thousands of Drupal websites now have backdoors; between ten and ninety percent of all Drupal websites. Automated Drupageddon exploits were in the wild within hours of the announcement. Updating or patching Drupal does not fix backdoors that attackers installed before updating or patching Drupal. Backdoors give attackers admin access and allow arbitrary PHP execution.
This is not a drill: Update Drupal 7 NOW
20 October 2014 - 2:53pm — BevanHalf of a client's Drupal 7 sites were compromised over the weekend.
If you did not update your Drupal 7 website by about Friday, your site was probably hacked too: Update to Drupal 7.32 or apply the patch manually updating is not trivial.
After that, you will need to review your site's administrator users, permissions, logs and content for unexpected users, roles, permissions, content and and scripts.